Immediate steps to protect sensitive data in the age of AI-driven threats
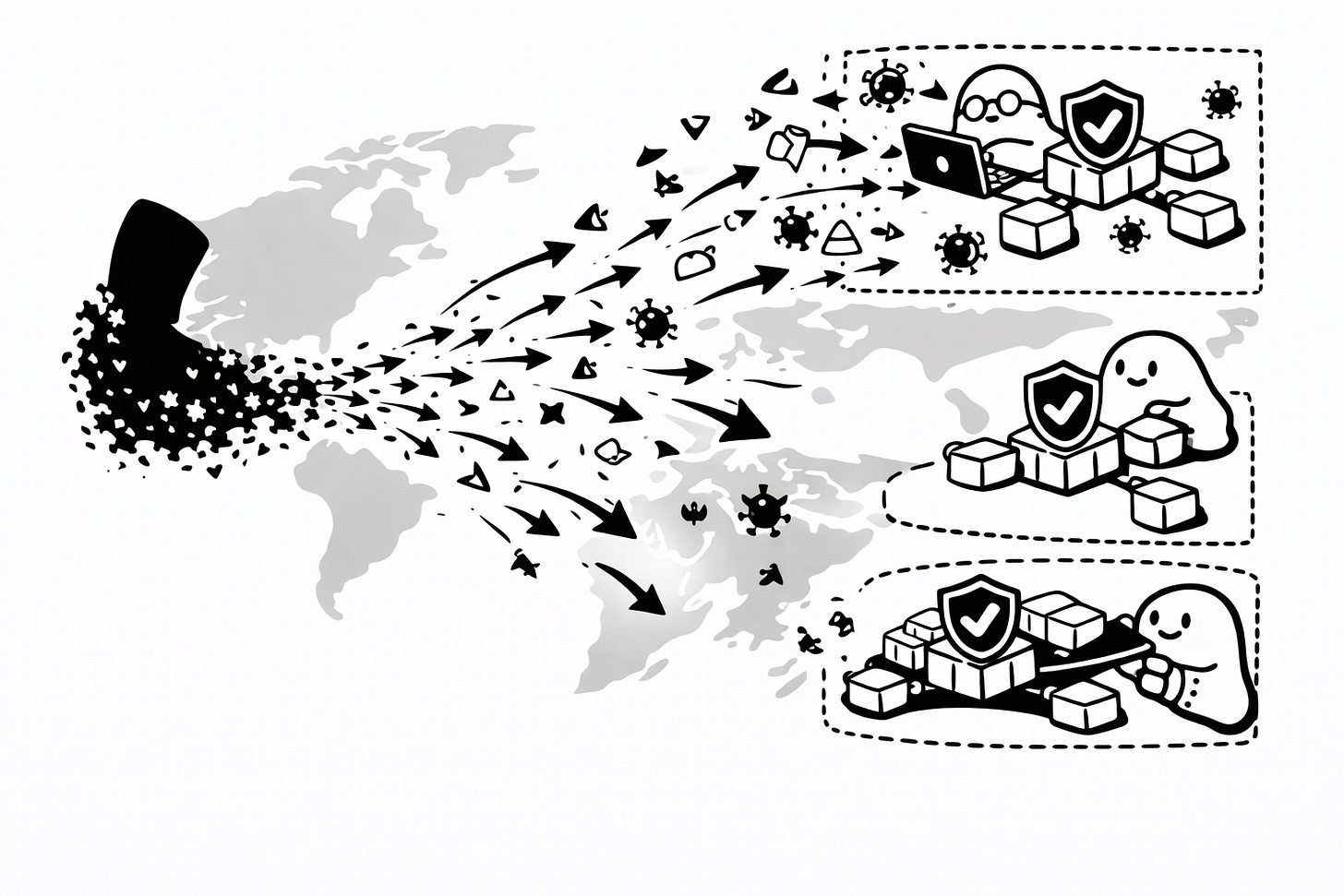
The recent Claude AI breach of Mexican government networks has demonstrated a new reality: AI is enabling attackers to scale their operations and craft sophisticated attacks faster than ever. Enterprises and government bodies can no longer rely solely on traditional security measures. Protecting sensitive data now requires a proactive, holistic approach.
1. Implement and enforce zero trust architecture (ZTA)
Zero Trust operates on a simple principle: never trust. Every system, communication, and user is treated as potentially compromised. Key aspects include:
Least-privilege access: Employees, contractors, and even executives should only have access to systems and data necessary for their role.
Formal frameworks: Follow standards like NIST SP 800-207, which provides a global benchmark for designing secure architectures.
A Zero Trust setup ensures that even if credentials are stolen or an employee is compromised, attackers cannot move freely within the network.
2. Enforce phishing-resistant multi-factor authentication (MFA).
Passwords alone are no longer sufficient. Organisations must deploy strong authentication methods to protect critical systems:
Hardware keys: Physical devices like YubiKeys provide strong protection against phishing and credential theft.
Passkeys and authenticator apps: Public/private key-based solutions and OTP apps add layers of security, reducing risks from stolen passwords.
3. Continuous monitoring and behavioural analytics
AI-powered attacks can move quickly, often bypassing traditional alerts. Continuous monitoring of network and user behaviour allows organisations to detect anomalies in real time and respond before breaches escalate.
4. Encrypt data at rest and in transit.
Encryption ensures that even if attackers gain access to systems, the information remains unreadable and unusable. This includes sensitive tax, voter, and employee data in government systems, as well as proprietary business data in enterprises.
The bottom line
The Claude AI incident is a warning: attacks are evolving, and AI can empower even lone attackers. Enterprises and government bodies must assume breaches are inevitable and design systems that minimise impact. Implementing Zero Trust, strong authentication, continuous monitoring, and encryption is no longer optional; it’s essential for safeguarding sensitive data in a world of AI-driven threats.
Get a quote for your project, schedule a call with our team, follow us on X, and sign up for our newsletter for simplified and curated Web3 security insights.