How to prepare your protocol for a secure token generating event (TGE)
A Token Generating Event (TGE) is when a protocol’s token goes live and becomes tradable. It enters the financial world.
Before TGE, the financial damage is limited. After TGE, real money, real users, and real attackers appear simultaneously. Incentives change. Liquidity increases. Mistakes become hard or impossible to undo.
Successful launches are rarely defined by one technical choice. They depend on whether security was treated as an ongoing process, not a final checkbox.
A secure TGE starts with a simple assumption: what can go wrong will go wrong. In a perfect world, there are no mistakes. In practice, you have to plan for failure. The goal is to detect problems early, understand them quickly, and limit their impact.
Security assurance and incident preparedness
Security assurance and incident preparedness focus on two things:
Reducing the chances of exploitation
Making sure the team can respond quickly and clearly when issues arise
At TGE, the security team must simultaneously limit how the protocol can be attacked and ensure a quick response to issues.
Limit how the protocol can be attacked
Enable fast detection, decision-making, and response
This requires security to cover the entire system. It must include design, development, deployment, and live operations. A final audit alone is not enough. If prevention or response is missing, small issues can quickly escalate into serious incidents once economic incentives are in place.
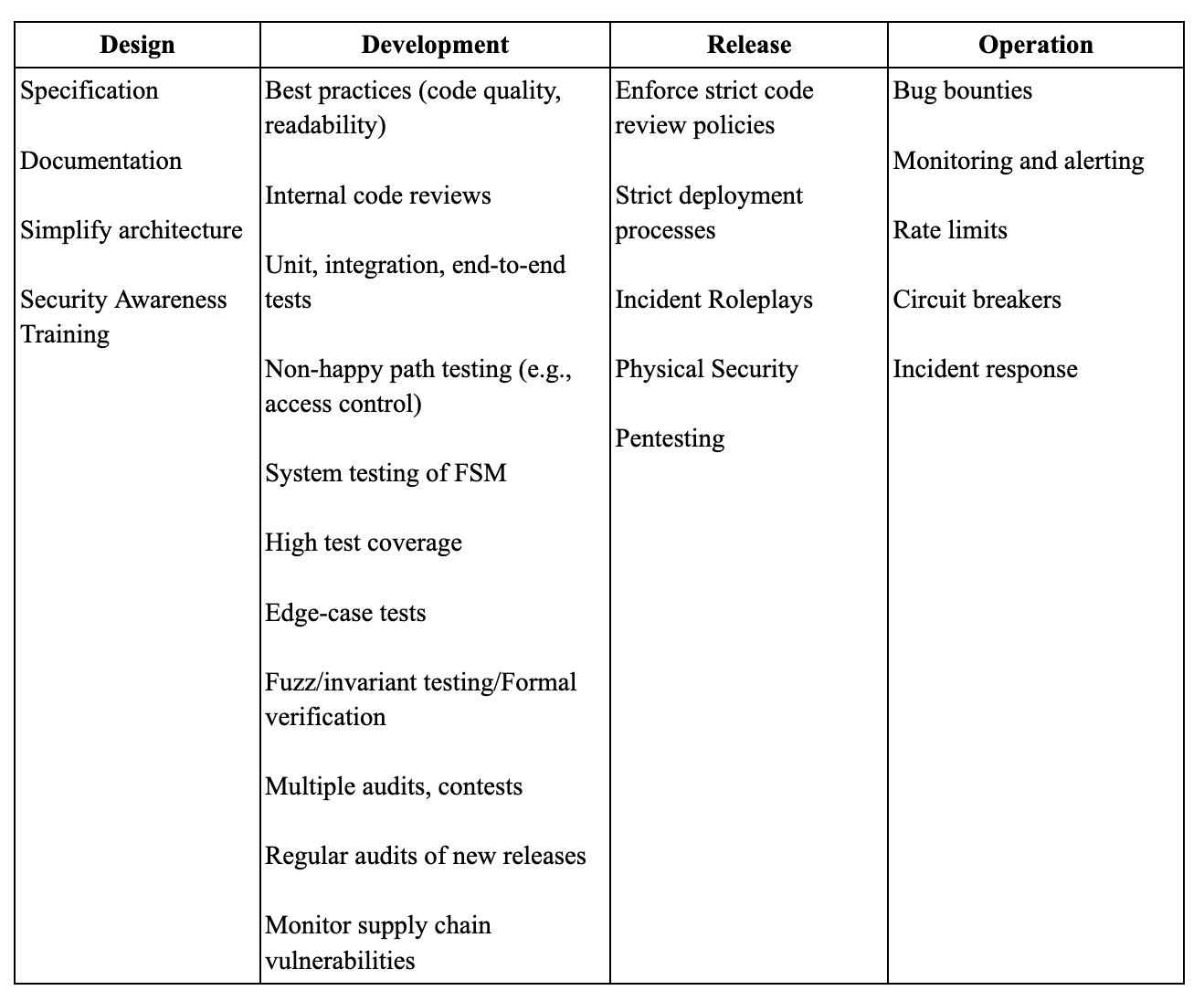
Security is a lifecycle process
Security is not a single tool or approval. It is a set of controls applied throughout the protocol’s lifecycle.
Each control helps, but none are perfect. By applying protections across Design→ Development → Release→ Operation, teams avoid relying on a single line of defence.
The most effective security work happens early. Issues found during design or development are easier and cheaper to fix. Controls in production exist to detect and contain problems that still occur after launch.
This approach assumes mistakes will happen. It is built to handle them.
No single control is enough on its own. Using multiple layers ensures problems are caught early and contained before they escalate. Read more on the “Swiss Cheese Model” of Cybersecurity.
TGE security readiness checklist
Principles are not enough. Teams need a practical checklist.
The TGE security readiness checklist turns this lifecycle approach into clear tasks. It is intended for use in the weeks before TGE as a working document, not a one-time review.
The checklist covers:
Architecture and documentation accuracy
Threat modelling and safety procedures
Upgrade mechanisms and emergency controls
Monitoring across contracts, infrastructure, and markets
Team access controls and security practices
Testing depth and coverage
Audit, pentesting, and bug bounty readiness
Launch-day incident planning and escalation
The checklist is available as a downloadable PDF, allowing teams to track ownership, progress, and readiness.
Download the security assurance & incident preparedness checklist to include it in your TGE plan.
Deliverables and support
The protocol team is responsible for core security work, including:
Testing
Documentation (Web2, Web3, and other components e.g. access to banking, etc.)
Security Architecture
Oak Security supports teams before and during TGE with both strategic and hands-on security services. This includes:
Security Strategy, including vendor selection
Threat models, audits, operational security training
Virtual CISO Services
Incident response runbook and escalation tree
For higher-risk launches, additional support may include:
Launch-day war room plan - technical & market incidents
Incident response team
Monitoring solutions setup
Physical security training/inspection of offices
The protocol team typically coordinates these efforts, with Oak providing guidance and oversight.
A secure TGE depends on three things: clear ownership, layered security, and rapid response. Getting these right before launch is what keeps small issues from becoming major incidents.
Get a quote for your project, schedule a call with our team, follow us on X, and sign up for our newsletter for simplified and curated Web3 security insights.